[Latest Updates] Cisco CCNP Security 300-206 Exam Practice Questions and answers,300-206 dumps free
Latest updates Cisco CCNP Security Implementing Cisco Edge Network Security Solutions (SENSS v1.0) 300-206 exam questions and Answers! Free sharing 300-206 pdf online download, online exam Practice test, easy to improve skills! Get the full 300-206 exam dumps: https://www.leads4pass.com/300-206.html (Total questions:358 Q&A). Year-round updates! guarantee the first attempt to pass the exam!
[PDF] Free Cisco 300-206 pdf dumps download from Google Drive: https://drive.google.com/open?id=1Fi5dnXk7rMDP8fptBfxwC4gFUayiB1VE
[PDF] Free Full Cisco pdf dumps download from Google Drive: https://drive.google.com/open?id=1CMo2G21nPLf7ZmI-3_hBpr4GDKRQWrGx
300-206 SENSS – Cisco: https://www.cisco.com/c/en/us/training-events/training-certifications/exams/current-list/specialist-senss.html
Latest effective Cisco 300-206 Exam Practice Tests
QUESTION 1
What are two security features at the access port level that can help mitigate Layer 2 attacks? (Choose two.)
A. DHCP snooping
B. IP Source Guard
C. Telnet
D. Secure Shell
E. SNMP
Correct Answer: AB
QUESTION 2
Choose two correct statements about private-vlan.
A. Interface that is assigned to primary-vlan ID (access mode) can communicate with interface with secondary vlan ID
that belongs to same primary-vlan (same switch)
B. Interface that is assigned to community vlan can communicate with interface in the same secondary vlan but it is also
configured as protected (same switch)
C. You have to configure dhcp snooping for both primary and secondary VLANs
D. You have to configure DAI only for primary vlan
E. You cannot combine private-vlan feature with protected ports ?
Correct Answer: DE
You can enable DHCP snooping on private VLANs. When you enable DHCP snooping on the primary VLAN, it is
propagated to the secondary VLANs. If you configure DHCP snooping on a secondary VLAN, the configuration does not
take
effect if the primary VLAN is already configured. The same statement is true about DAI.
A private-VLAN port cannot be a secure port and should not be configured as a protected port.
QUESTION 3
What command alters the SSL ciphers used by the Cisco Email Security Appliance for TLS sessions and HTTPS
access?
A. sslconfig
B. sslciphers
C. tlsconifg
D. certconfig
Correct Answer: A
QUESTION 4
When you set a Cisco IOS Router as an SSH server, which command specifies the RSA public key of the remote peer
when you set the SSH server to perform RSA-based authentication?
A. router(config-ssh-pubkey-user)#key
B. router(conf-ssh-pubkey-user)#key-string
C. router(config-ssh-pubkey)#key-string
D. router(conf-ssh-pubkey-user)#key-string enable ssh
Correct Answer: B
QUESTION 5
Where do you apply a control plane services policy to implement Management Plane Protection on a Cisco Router?
A. Control-plane router
B. Control-plane host
C. Control-plane interface management 0/0
D. Control-plane service policy
Correct Answer: B
http://www.cisco.com/c/en/us/td/docs/ios/12_4t/12_4t11/htsecmpp.html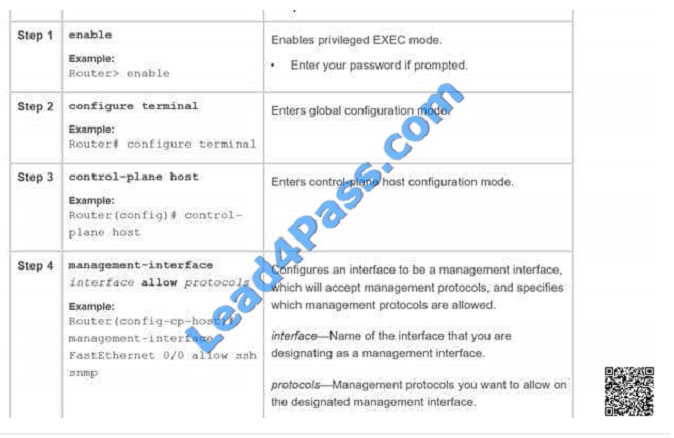
QUESTION 6
Which three statements about private VLANs are true? (Choose three.)
A. Isolated ports can talk to promiscuous and community ports.
B. Promiscuous ports can talk to isolated and community ports.
C. Private VLANs run over VLAN Trunking Protocol in client mode.
D. Private VLANS run over VLAN Trunking Protocol in transparent mode.
E. Community ports can talk to each other as well as the promiscuous port.
F. Primary, secondary, and tertiary VLANs are required for private VLAN implementation.
Correct Answer: BDE
QUESTION 7
Which option is the Cisco ASA on-box graphical management solution?
A. SSH
B. ASDM
C. Console
D. CSM
Correct Answer: B
QUESTION 8
Which three options describe how SNMPv3 traps can be securely configured to be sent by IOS? (Choose three.)
A. An SNMPv3 group is defined to configure the read and write views of the group.
B. An SNMPv3 user is assigned to SNMPv3 group and defines the encryption and authentication credentials.
C. An SNMPv3 host is configured to define where the SNMPv3 traps will be sent.
D. An SNMPv3 host is used to configure the encryption and authentication credentials for SNMPv3 traps.
E. An SNMPv3 view is defined to configure the address of where the traps will be sent.
F. An SNMPv3 group is used to configure the OIDs that will be reported.
Correct Answer: ABC
QUESTION 9
What is the maximum jumbo frame size for IPS standalone appliances with 1G and 10G fixed or add-on interfaces?
A. 1024 bytes
B. 1518 bytes
C. 2156 bytes
D. 9216 bytes
Correct Answer: D
QUESTION 10
Which technology can be deployed with a Cisco ASA 1000V to segregate Layer 2 access within a virtual cloud
environment?
A. Cisco Nexus 1000V
B. Cisco VSG
C. WSVA
D. ESVA
Correct Answer: A
QUESTION 11
With Cisco ASA active/standby failover, by default, how many monitored interface failures will cause failover to occur?
A. 1
B. 2
C. 3
D. 4
E. 5
Correct Answer: A
QUESTION 12
You are going to add ASA to CSM (Cisco Security Manager). Which port on ASA must be reachable for CSM to
succeed?
A. 21
B. 22
C. 80
D. 443
Correct Answer: D
Security Manager can use these transport protocols:
SSL (HTTPS)–Secure Socket Layer, which is an HTTPS connection, is the only transport protocol used with PIX
Firewalls, Adaptive Security Appliances (ASA), and Firewall Services Modules (FWSM). It is also the default protocol for
IPS
devices and for routers running Cisco IOS Software release 12.3 or higher.
If you use SSL as the transport protocol on Cisco IOS routers, you must also configure SSH on the routers. Security
Manager uses SSH connections to handle interactive command deployments during SSL deployments. Cisco Security
Manager was using OpenSSL for the Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols.
Beginning with version 4.13, Cisco Security Manager replaced OpenSSL version 1.0.2 with Cisco SSL version 6.x.
Cisco SSL
enables FIPS compliance over full FIPS Validation which results in fast and cost-effective connectivity. The Common
Criteria mode in Cisco SSL allows easier compliance. Cisco SSL is feature-forward when compared to OpenSSL. The
product Security Baseline (PSB) requirements for Cisco SSL ensures important security aspects such as credential and
key management, cryptography standards, antispoofing capabilities, integrity and tamper protection, and session, data,
and stream management and administration are taken care of.
SSH–Secure Shell is the default transport protocol for Catalyst switches and Catalyst 6500/7600 devices. You can also
use it with Cisco IOS routers.
Telnet–Telnet is the default protocol for routers running Cisco IOS software releases 12.1 and
12.2. You can also use it with Catalyst switches, Catalyst 6500/7600 devices, and routers running Cisco IOS Software
release 12.3 and higher. See the Cisco IOS software documentation for configuring Telnet.
HTTP–You can use HTTP instead of HTTPS (SSL) with IPS devices. HTTP is not the default protocol for any device
type.
TMS–Token Management Server is treated like a transport protocol in Security Manager, but it is not a real transport
protocol. Instead, by configuring TMS as the transport protocol of a router, you are telling Security Manager to deploy
configurations to a TMS. From the TMS, you can download the configuration to an eToken, plug the eToken into the
router\\’s USB bus, and update the configuration. TMS is available only for certain routers running Cisco IOS Software
12.3 or
higher.
Security Manager can also use indirect methods to deploy configurations to devices, staging the configuration on a
server that manages the deployment to the devices. These indirect methods also allow you to use dynamic IP
addresses on
your devices. The methods are not treated as transport protocols, but as adjuncts to the transport protocol for the
device. You can use these indirect methods:
AUS (Auto Update Server)–When you add a device to Security Manager, you can select the AUS server that is
managing it. You can use AUS with PIX Firewalls and ASA devices.
Configuration Engine–When you add a router to Security Manager, you can select the Configuration Engine that is
managing it.
QUESTION 13
What are two enhancements of SSHv2 over SSHv1? (Choose two.)
A. VRF-aware SSH support
B. DH group exchange support
C. RSA support
D. keyboard-interactive authentication
E. SHA support
Correct Answer: AB
QUESTION 14
Which two commands can be used to create a Cisco Unified ACL within the ASA CLI? (Choose two.)
A. ipv6 access-list
B. object-group network
C. ipv6 access-list webtype
D. access-list extended
E. object-group network nat-pat-grp
Correct Answer: BD
https://www.cisco.com/c/en/us/td/docs/security/asa/asa90/configuration/guide/asa_90_cli_config/acl_extended.pdf
QUESTION 15
Which statement about Cisco IPS Manager Express is true?
A. It provides basic device management for large-scale deployments.
B. It provides a GUI for configuring IPS sensors and security modules.
C. It enables communication with Cisco ASA devices that have no administrative access.
D. It provides greater security than simple ACLs.
Correct Answer: B
QUESTION 16
What is the default log level on the Cisco Web Security Appliance?
A. Trace
B. Debug
C. Informational
D. Critical
Correct Answer: C
QUESTION 17
Which two option are main challenges for public cloud data center?
A. deployment cost
B. tenant isolation
C. disaster recovery
D. system scalability
E. network visibility
Correct Answer: BE
QUESTION 18
If you encounter problems logging in to the Cisco Security Manager 4.4 web server or client or backing up its databases,
which account has most likely been improperly modified?
A. admin (the default administrator account)
B. casuser (the default service account)
C. guest (the default guest account)
D. user (the default user account)
Correct Answer: B
QUESTION 19
Which Cisco TrustSec role does a Cisco ASA firewall serve within an identity architecture?
A. Access Requester
B. Policy Decision Point
C. Policy Information Point
D. Policy Administration Point
E. Policy Enforcement Point
Correct Answer: E
QUESTION 20
Which statement about Cisco Security Manager form factors is true?
A. Cisco Security Manager Professional and Cisco Security Manager UCS Server Bundles support FWSMs.
B. Cisco Security Manager Standard and Cisco Security Manager Professional support FWSMs.
C. Only Cisco Security Manager Professional supports FWSMs.
D. Only Cisco Security Manager Standard supports FWSMs.
Correct Answer: A
QUESTION 21
If a switch port goes directly into a blocked state only when a superior BPDU is received, what mechanism must be in
use?
A. STP bpdu guard
B. STP root guard
C. SPT bpdu filter
Correct Answer: B
QUESTION 22
Refer to the exhibit. Why was the packet dropped? ****Exhibit is Missing****
(this exhibit is packet capture with traffic destination to port 23 and being drop by access- list)
A. Telnet access is not allowed between these two nodes.
B. NAT is not applied correctly for the 10.10.96.5 host
C. The source port is configured incorrectly In the capture
D. There is no route on the Cisco ASA to the destination host
Correct Answer: A
QUESTION 23
A network engineer must mange and configurations to a cisco networking environment solutions accomplishes this
task?
A. cisco IPS manage express and pushing configuration to the ips units
B. cisco security 4.5 or later and pushing configuration bundles to each of the,,,,,
C. cisco adaptive security device manager to push configuration to each of the IPS
D. fire SIGHT manager to bundle and push configuration to the IPS units installed
Correct Answer: D
QUESTION 24
A network administrator is creating an ASA-CX administrative user account with the following parameters:
– The user will be responsible for configuring security policies on network devices.
–
The user needs read-write access to policies.
–
The account has no more rights than necessary for the job.
What role will the administrator assign to the user?
A. Administrator
B. Security administrator
C. System administrator
D. Root Administrator
E. Exec administrator
Correct Answer: B
QUESTION 25
Which Cisco product provides a GUI-based device management tool to configure Cisco access routers?
A. Cisco ASDM
B. Cisco CP Express
C. Cisco ASA 5500
D. Cisco CP
Correct Answer: D
QUESTION 26
Which are the most secure authentication and encryption options? (Choose two)
A. DES
B. 3DES
C. AES
D. MD5
E. SHA
Correct Answer: CE
https://www.cisco.com/c/en/us/about/security-center/next-generation-cryptography.html#2
QUESTION 27
Which policy map action makes a Cisco router behave as a stateful firewall for matching traffic?
A. Log
B. Inspect
C. Permit
D. Deny
Correct Answer: B
QUESTION 28
What two are data and voice protocols do ASA 5500 supports? (Choose two)
A. CTIQBE Inspection
B. H.323 Inspection
C. MGCP Inspection
D. RTSP Inspection
E. SIP Inspection
F. Skinny (SCCP) Inspection
Correct Answer: BD
QUESTION 29
A. choosed to use udp as answer
Correct Answer: A
QUESTION 30
About User identity with domain (there is a screen), if user is not in domain, what identity will be?
A. local
B. default
Correct Answer: A
ASA Identity Firewal:
The default domain is used for all users and user groups when a domain has not been explicitly configured for those
users or groups. When a default domain is not specified, the default domain for users and groups is LOCAL.
Additionally, the
Identity Firewall uses the LOCAL domain for all locally defined user groups or locally defined users (users who log in
and authenticate by using a VPN or web portal).
QUESTION 31
Refer to the exhibit. Which statement about this access list is true?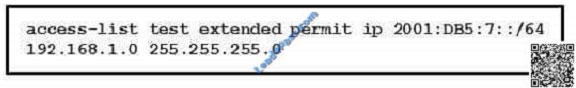
A. This access list does not work without 6to4 NAT
B. IPv6 to IPv4 traffic permitted on the Cisco ASA by default
C. This access list is valid and works without additional configuration
D. This access list is not valid and does not work at all
E. We can pass only IPv6 to IPv6 and IPv4 to IPv4 traffic
Correct Answer: A
ASA 9.0(1) code introduced the Unified ACL for IPv4 and IPv6. ACLs now support IPv4 and IPv6 addresses. You can
even specify a mix of IPv4 and IPv6 addresses for the source and destination. The any keyword was changed to
represent IPv4 and IPv6 traffic. The any4 and any6 keywords were added to represent IPv4-only and IPv6-only traffic,
respectively. The IPv6-specific ACLs are deprecated. Existing IPv6 ACLs are migrated to extended ACLs.
QUESTION 32
Which kind of Layer 2 attack targets the STP root bridge election process and allows an attacker to control the flow of
traffic?
A. man-in-the-middle
B. denial of service
C. distributed denial of service
D. CAM overflow
Correct Answer: A
QUESTION 33
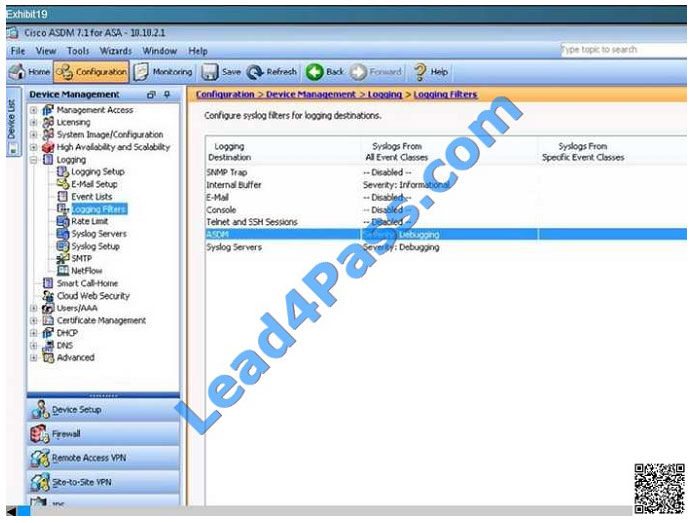
Hotspot Question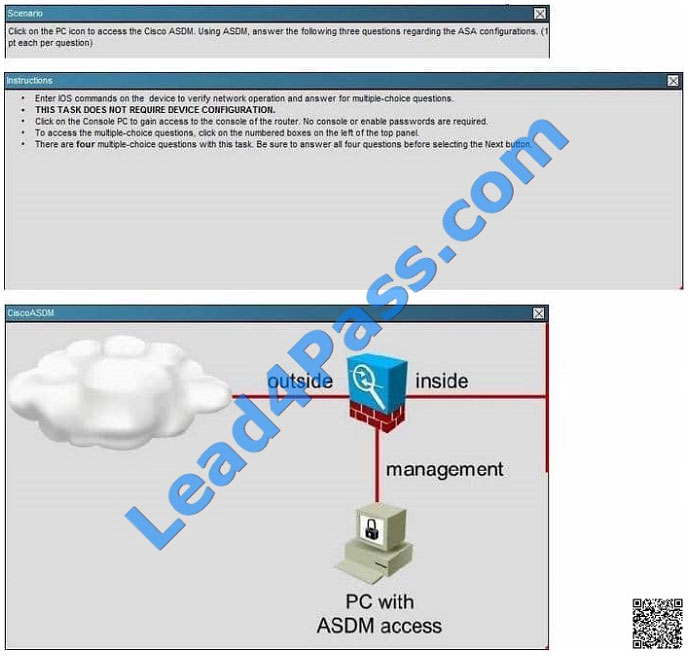
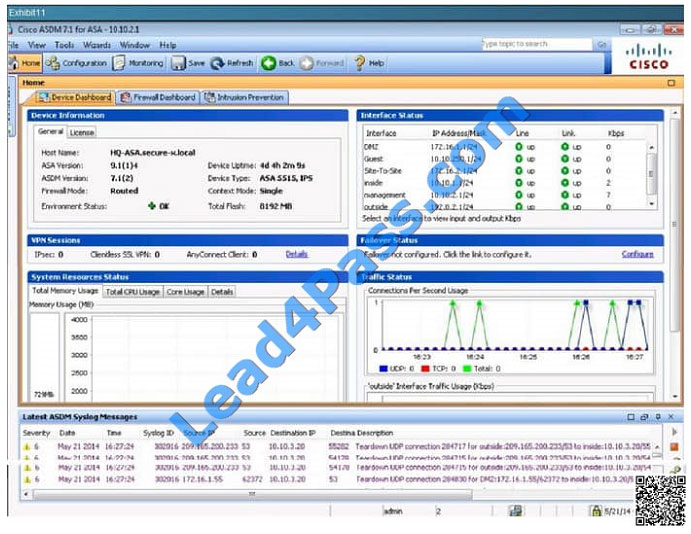
Which statement is true of the logging configuration on the Cisco ASA?
A. The contents of the internal buffer will be saved to an FTP server before the buffer is overwritten.
B. The contents of the internal buffer will be saved to flash memory before the buffer is overwritten.
C. System log messages with a severity level of six and higher will be logged to the internal buffer.
D. System log messages with a severity level of six and lower will be logged to the internal buffer.
Correct Answer: C 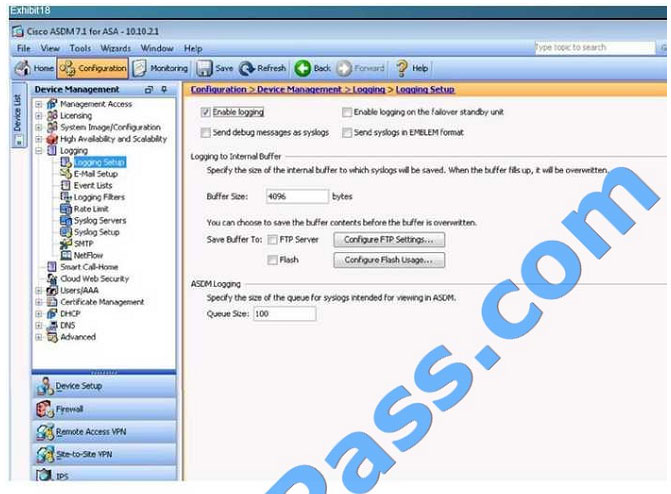
QUESTION 34
When you install a Cisco ASA AIP-SSM, which statement about the main Cisco ASDM home page is true?
A. It is replaced by the Cisco AIP-SSM home page.
B. It must reconnect to the NAT policies database.
C. The administrator can manually update the page.
D. It displays a new Intrusion Prevention panel.
Correct Answer: D
QUESTION 35
Which of the following that Cisco engineer must secure a current monitoring environment? (Choose Two)
A. RSA-SIG
B. MD5
C. AES
D. 3DES
E. DES
Correct Answer: CD
QUESTION 36
You must restrict the interface on which management traffic can be received by the routers on your network. Which
feature do you enable?
A. MPP
B. extended ACL on all of the interfaces
C. CPP with a port filter
D. AAA
Correct Answer: A
QUESTION 37
Which statement about static or default route on the Cisco ASA appliance is true?
A. The admin distance is 1 by default.
B. From the show route output, the [120/3] indicates an admin distance of 3.
C. A default route is specified using the 0.0.0.0 255.255.255.255 address/mask combination.
D. The tunneled command option is used to enable route tracking.
E. The interface-name parameter in the route command is an optional parameter if the static route points to the next-
hop router IP address.
Correct Answer: A
QUESTION 38
Which Cisco prime Infrastructure features allows you to assign templates to a group of wireless LAN controllers with
similar configuration requirements?
A. Lightweight access point configuration template
B. Composite template
C. Controller configuration group
D. Shared policy object
Correct Answer: C
QUESTION 39
CORRECT TEXT
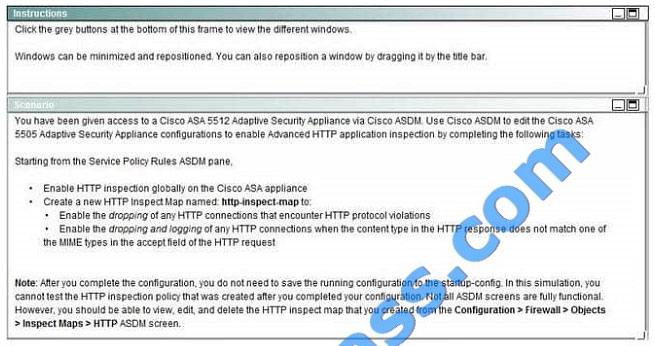
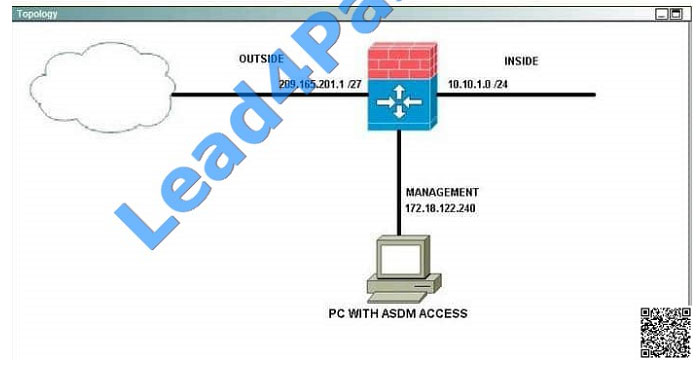
Correct Answer: explanation
Answer: Please check the steps in explanation part below:
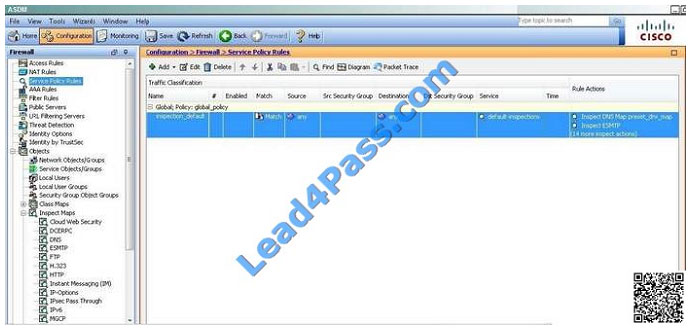
1) Click on Service Policy Rules, then Edit the default inspection rule.
2) Click on Rule Actions, then enable HTTP as shown here: 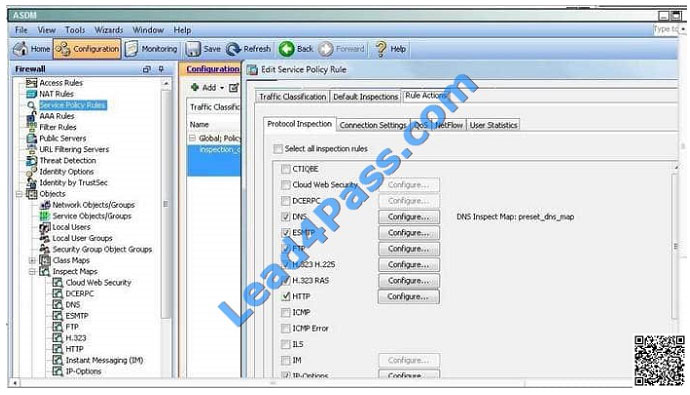
3) Click on Configure, then add as shown here: 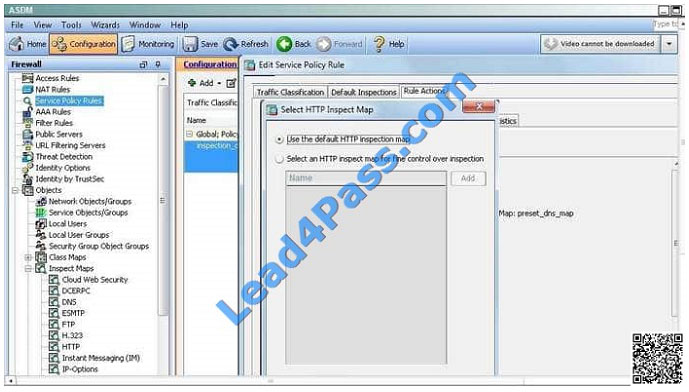
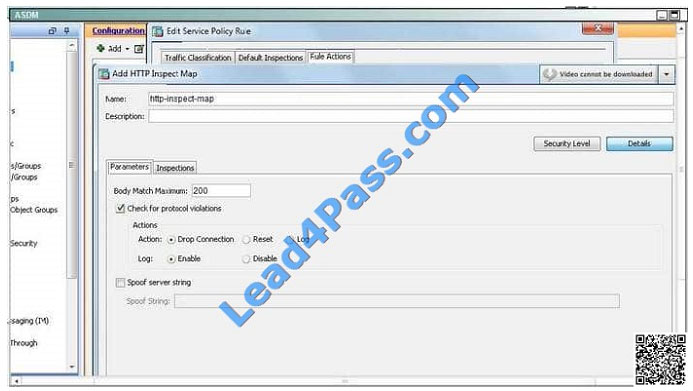
4) Create the new map in ASDM like shown: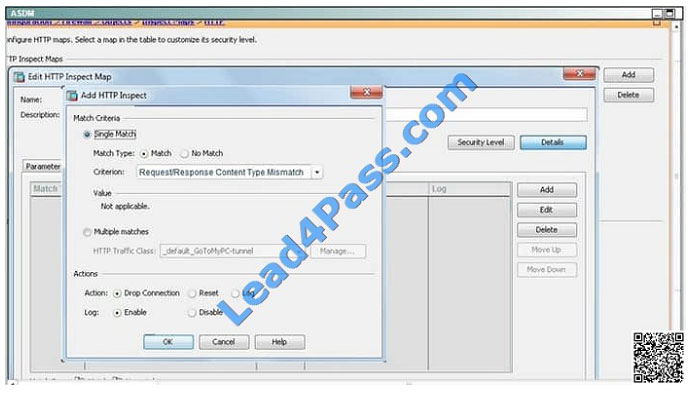
5) Edit the policy as shown:
6) Hit OK
QUESTION 40
Refer to the exhibit. Which Cisco ASA CLI commands configure these static routes in the Cisco ASA routing table?
S 10.2.2.0 255.255.255.0 [1/0] via 172.16.1.10, dmzS 10.3.3.0 255.255.255.0 [2/0] via 172.16.1.11, dmz
A. route dmz 10.2.2.0 0.0.0.255 172.16.1.10 route dmz 10.3.3.0 0.0.0.255 172.16.1.11
B. route dmz 10.2.2.0 0.0.0.255 172.16.1.10 1 route dmz 10.3.3.0 0.0.0.255 172.16.1.11 1
C. route dmz 10.2.2.0 0.0.0.255 172.16.1.10 route dmz 10.3.3.0 0.0.0.255 172.16.1.11 2
D. route dmz 10.2.2.0 255.255.255.0 172.16.1.10 route dmz 10.3.3.0 255.255.255.0 172.16.1.11
E. route dmz 10.2.2.0 255.255.255.0 172.16.1.10 1 route dmz 10.3.3.0 255.255.255.0 172.16.1.11 1
F. route dmz 10.2.2.0 255.255.255.0 172.16.1.10 route dmz 10.3.3.0 255.255.255.0 172.16.1.11 2
Correct Answer: F
We offer more ways to make it easier for everyone to learn, and YouTube is the best tool in the video.
Follow channels: https://www.youtube.com/channel/UCXg-xz6fddo6wo1Or9eHdIQ/videos get more useful exam content.
Latest Cisco 300-206 YouTube videos:
This is the latest update released by the Cisco CCNP Security Implementing Cisco Edge Network Security Solutions (SENSS v1.0) 300-206 exam questions and answers, and we share 40 exam questions and answers for free to help you improve your skills! You can download 300-206 pdf or watch the 300-206 YouTube video tutorial online! Get the full 300-206 exam dumps: https://www.leads4pass.com/300-206.html (Total questions:358 Q&A). Help you pass the exam quickly!
[PDF] Free Cisco 300-206 pdf dumps download from Google Drive: https://drive.google.com/open?id=1Fi5dnXk7rMDP8fptBfxwC4gFUayiB1VE
[PDF] Free Full Cisco pdf dumps download from Google Drive: https://drive.google.com/open?id=1CMo2G21nPLf7ZmI-3_hBpr4GDKRQWrGx
Lead4pass Promo Code 12% Off
We share more practical and effective exam dumps (Cisco,Microsoft,Oracle,Citrix,Comptia…) The latest citrix 1y0-a20 exam dumps help you improve your skills